




In this episode of What’s in the SOSS, we sit down with the OpenSSF’s new General Manager, Steve Fernandez — a seasoned enterprise tech leader whose resumé spans giants like L’Oréal, Coca-Cola, AIG, and Ford. Steve shares his “origin story,” what drew him into the world of open source, and how his decades of experience as a consumer of open source software are shaping his vision for the Foundation.
00:21 Welcome & Introductions
00:57 Steve’s Tech Journey
03:13 Why OpenSSF?
05:02 The Role of Security & Strategic Vision
08:17 Rapid Fire & Final Thoughts
CRob (00:21)
Welcome, welcome, welcome. This is What’s in the SOSS, the OpenSSF’s podcast where we talk to developers, industry experts, and assorted amazing people within our open source ecosystem. I’m CRob, one of your co-hosts for this little event. I do security stuff on the internet, and today we have a new friend to introduce the world to, Steve Fernandez, who just recently joined the foundation.
And Steve, maybe you could talk a little bit about, introduce yourself and maybe talk about your technology origin story.
Steve Fernandez (00:57)
Thanks a lot and great introduction, by the way. So pleasure to meet everybody. My name is Steve Fernandez and as CRob mentioned, I’m the new general manager for the OpenSSF. And I come to this place through a long IT journey. For the last 30 years, I’ve been mainly on the enterprise side of the IT game.
I’ve done various roles as CIO and CTO in many different industries as well as many different companies. Most recently, before I came to the OpenSSF, I was the CIO for NCR Voyix, and previous to that, I was Chief Technology Officer for L’Oreal in Paris, Chief Technology Officer for AIG in the insurance industry.
I was chief technology officer at Coca-Cola and then I worked many years inside of GE and Ford Motor Company in different technology roles. So I really come to this job, I think, with a different and unique perspective than many who’ve been in the open source world for forever. I’m coming as a user of the open source and it’s been a user of the software and the technology inside of all the platforms that I’ve run and managed over the last 30 years. So I’m very excited to take a little different view of technology in this role and hoping a lot of my experience from running enterprise and running large scale platforms and running things day to day is going to translate into growth for the organization and further stability as we move forward.
CRob (02:43)
And, we’ve cited here and at other events, just the penetration of open source in normal operations and just how critical open source is to a lot of enterprises. So I’m very excited to kind of benefit from the experiences you’ve had in your long and successful career and trying to help bring that more business focus to us. But I’m curious, what drew you to the OpenSSF? Was it the goose?
Steve Fernandez (03:13)
I think it could have been the goose, which is quite the great icon. You know, it was a, it’s really interesting for me personally. I was getting to a point in my life where I’ve done many, many operational roles throughout my life and my career. And I was taking a little break and trying to figure out what I wanted to do when I grow up and what I wanted to do next on the journey. And, you know, it’s one of those small things, a friend of a friend talked to me about this position and I said, hmm being general manager of a foundation. Well, I can at least take a look and see what it’s about. And, and, uh, I don’t know, it’s something I’ve never done before, but I think it might make sense. So I sat down with, uh, Jim Zemlin, uh, head of the Linux foundation. And we just had a great conversation and being an open source user throughout my career and knowing the importance of open source and security you know, to every company’s platform, to every company’s install base. It really was a job that I was looking for where I thought I could do some good for the community. I thought I could, like I said earlier, take a different perspective on things, add a little bit of my corporate background to the organization and merge the two together.
Steve Fernandez (04:31)
So for me, it was really about trying something new, experimenting – bring a little bit of your old experience into a new environment. And I have to say, in just the last month that I’ve been here, it’s been an exceptional experience and working with absolutely great people, working with a great community. So, so far it’s been a really, really positive experience and a bit different from my enterprise days, but at the same time, very exciting and it’s great to be involved in real technology.
CRob (05:02)
So it’s interesting you have a long history of kind of helping lead technology organizations. From your perspective, how have you seen security kind of help the business and how does security help developers and other consumers?
Steve Fernandez (05:18)
Yeah, so I’ve always called security kind of the hidden greatness. It’s one of those things that you don’t know you need security until you know you need security.
CRob (05:30) Yeah.
Steve Fernandez (05:31)
And on the enterprise side of the game, it’s your constant worry about security and risk. And you’re always worrying about your platforms. You’re always worried about your products. You’re always worried about making sure that things that you’re presenting to the consumer or to the employee or to, you know, the different install bases, you have an inherent need to make sure your products and your technology are secure. So I’ve always had a love hate with it because you hate to spend incredible amounts of time and investment in security, but you absolutely love it because it keeps you safe and, and, and makes sure that your products and your technology are going to…with it – you know, there are bad actors out there and people do want to get into your products. They do want to find out, you know, personal information. So security is that thing that makes us feel a little bit better. And it lowers your risk profile. And, you know, it’s really the glue that’s needed inside of a technology base.
CRob (06:37)
Mm-hmm.
And thinking about your experiences in your past roles, what do you see, kind of, the additional value and capabilities you’re going to bring to the foundation to help us further our mission?
Steve Fernandez (06:51)
Well, I’m thinking, you what I found in the foundation last month and working with people is we have an incredible set of people and we have an incredible set of technical sales and also have like a really unique community that works together in, you know, in a matrix like organization, but it really works and people are all, you know, moving forward to do what they think is the right thing.
I think what I’m going to try to bring to the foundation from my past is a little bit of strategic vision, a little bit of process, a little bit of thought process at a methodical level so that we best utilize the people that we have and the capabilities that we have. One of the great things I felt as I came into the organization and I’ve been doing my original first month assessment is, you know, we don’t have to reinvent the wheel. We just got to get efficient. We got to make sure our priorities are in line. We need to make sure we work with our enterprise partners. We need to make sure we work with our development community. And I think my job is going to be bringing those different pieces together and working a little bit more seamlessly.
So, that’s really, think, where I’ll add value and a little bit of my past will help out the organization.
CRob (08:17)
Excellent. Well, I can say personally, I’m very excited to be collaborating with you on this mission. And I know our community is very excited to be working with you. But let’s move on to the rapid fire part of our session. Are you ready for rapid, rapid, rapid fire? I got a couple of wacky questions I’m going to ask you just off the cuff answers. What’s your favorite vegetable?
Steve Fernandez (08:40)
Broccoli
CRob (08:42)
Okay, that is a perfectly fine vegetable. Thinking about the amazing open source ecosystem, what’s your favorite open source mascot?
Steve Fernandez (08:51)
The Goose.
CRob (08:53)
The goose, that’s an excellent answer. And mild or spicy food?
Steve Fernandez (08:59)
Spicy as it can get.
CRob (09:00)
Ohhhh, that’s spicy. Nice. And final and probably most important question. Star Trek or Star Wars?
Steve Fernandez (09:11)
Gotta go Trek.
CRob (09:12)
Excellent. Both answers are great, but that’s a fine, fine answer. Thank you, thank you. Well, Steve, as we wind down, do you have any kind of parting thoughts, any words of wisdom that you want to share with our community?
Steve Fernandez (09:29)
You know, I just say to the community, mostly keep the passion alive that you have for the work you’re doing. It’s very apparent when somebody new to the community sees it, you know, especially like myself. I see the passion. I see the intelligence. I see the hard work. And I think you should all feel very proud about that work that you’re doing. It really shows and it’s really transparent to everybody.
So, you know, I’m here to work with you. I’m here to collaborate. I’m here to help drive whatever I can do to better the community. So in that spirit, just please be open with everybody. Feel free to contact me at any time if you have ideas or thoughts about how we can improve the community or how we can move forward. That’s very important to me and I want to work in this know, great environment and, you know, and really help it grow and really foster that security community that we built and continue to do so. So I just say keep working hard and it’s going great.
CRob (10:35)
Thank you very much Steve Fernandez. Thank you for joining us and thank you for spending your time today with what’s in the SOSS and to our audience Happy open sourcing. We’ll talk to you soon
(10:47)
Like what you’re hearing. Be sure to subscribe to What’s in the SOSS on Spotify, Apple Podcasts, antennapod, pocketcast or wherever you get your podcasts. There’s a lot going on with the OpenSSF and many ways to stay on top of it all. Check out the newsletter for open source news, upcoming events and other happenings. Go to openssf.org/newsletter to subscribe. Connect with us on LinkedIn for the most up-to-date OpenSSF news and insight and be a part of the OpenSSF community at openssf.org/getinvolved. Thanks for listening and we’ll talk to you next time on What’s in the SOSS.

By Christopher Robinson (CRob), Chief Security Architect, OpenSSF
VulnCon 2025 has once again proven to be an essential gathering for security professionals, fostering collaboration, innovation, and progress in vulnerability management. This matches well with the OpenSSF continued championing for transparency and best practices in open source security. Practitioners from around the world gathered in Raleigh, NC, the week of April 7-10, 2025 to share knowledge, collaborate, and raise awareness of key issues within the global vulnerability management ecosystem. We wanted to share my key takeaways from this year’s conference and highlight some of the insightful contributions from our community members.
The Open Source Security Foundation (OpenSSF) seeks to make it easier to sustainably secure the development, maintenance, and consumption of the open source software (OSS) we all depend on. We work on this by fostering collaboration with fellow industry groups like the CVE Program and FIRST, establishing best practices like our recently released Principles for Package Repository Security guide, and developing innovative solutions like Open Source Project Security Baseline, or engaging in global cybersecurity legislation and public policy conversations with our Global Cyber Policy Working Group. Cross-industry collaboration and knowledge sharing is crucial to properly address major challenges by fostering innovation, knowledge sharing, driving sustainable growth, and maximizing the impacts of our collective efforts.
The OpenSSF was thrilled to have a notable presence at VulnCon with significant representation from our Vulnerability Disclosures Working Group and other projects throughout the week. Our engagement in this event illustrates our commitment to community engagement and further supports our strategy to actively engage with the community and facilitate collaboration across industry stakeholders to sustainably address open source software security challenges effectively with transparent operations and governance.
The partnership between the OpenSSF and the FIRST PSIRT SIG showcases how industry and upstream effectively work together on these issues that have global impacts and how we’re better collectively collaborating to solve these complex and far-reaching challenges. Through our co-work on industry standards, and frameworks, or an event like VulnCon – we’re better together!
The inaugural VulnCon was a cross-industry effort that was held in March 2024. There were 360 security professionals in attendance, with an additional 239 participating virtually (599 total) with nearly 40 sessions given. 2025 saw a dramatic increase in the participants and volume of content shared! This year there were 448 in person attendees with 179 global friends watching and participating virtually (627 total). 294 organizations attended from 36 countries. The program itself almost doubled, adding a 4th full day of sessions and expanding the number of tracks provided up to 100 sessions. Of this, I am proud to say that the OpenSSF members provided over 16 sessions about our community’s work and 46 total sessions given by member representatives.
This year’s VulnCon featured an amazing docket of talks and workshops spanning the broad spectrum of vulnerability management, disclosure, and coordination. Open Source Software was discussed throughout the four day event, driving home to me how much influence and exposure upstream has on industry and public policy.
Here are a few of my key takeaways:
At the end of the day, security is about effectively managing risk and preparing for the inevitable threats that loom on the horizon. Events such as VulnCon or the forthcoming CNCF-OpenSSF SecurityCon allow experts to come together, share their hard-won wisdom, raise awareness of issues of concern, and collaborate on solutions to address security issues around the world.
The conversations at VulnCon reaffirm the importance of continued engagement in the security community. If you’re interested in contributing to the advancement of open source security, I encourage you to join the OpenSSF community.
Join the OpenSSF mailing list to stay informed about upcoming events, working groups, and initiatives.
For those who couldn’t make it, you can check out recorded content from VulnCon 2024 on YouTube and look out for the VulCon 2025 playlist to get a sense of the discussions shaping the future of vulnerability management. Thank you to all of our amazing community members who were able to come out and demonstrate the power of collaboration of our open source security community and partner with our peers and downstreams within industry, security research, and global governments.


Welcome to the March 2025 edition of the OpenSSF Newsletter! Here’s a roundup of the latest developments, key events, and upcoming opportunities in the Open Source Security community.
This month, the OpenSSF invites you to participate in global Community Days and explore new initiatives to strengthen open source security throughout 2025. Tune in to the latest podcast episode highlighting key insights from leaders at Intel and GitHub, learn about the recent Policy Summit in Washington, D.C., and enroll in the new, free cybersecurity course designed specifically for software development managers. Plus, stay informed about exciting project updates and upcoming community events!
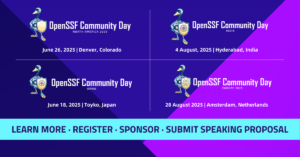
OpenSSF Community Days bring together security and open source experts to drive innovation in software security.
✅ Secure your spot – Register today!
✅ Have insights to share? Submit to speak before CFP closes!
✅ Support the mission – Become a sponsor!
Join us in shaping a safer and more secure digital world.

Cybersecurity is an ongoing challenge, and OpenSSF is leading efforts to strengthen open source security in 2025. This blog outlines the key content themes for the year, from strengthening OSS ecosystems to enhancing security tools and addressing vulnerabilities. Each month, OpenSSF will explore these critical topics through events, expert discussions, and blog contributions. Stay updated on these discussions and learn how you can contribute to OpenSSF’s mission.

In Season 2’s first episode, CRob chats with Arun Gupta (Intel, OpenSSF Governing Board Chair) and Zach Steindler (GitHub, OpenSSF TAC Chair) about lessons learned in open source security from 2024 and what’s ahead for 2025.
Join the conversation and get insights into the future of open source security. Listen now and stay tuned as we announce our new co-host!

The OpenSSF successfully hosted the 2025 Policy Summit in Washington, D.C., bringing together industry leaders and security experts to address open source security challenges. The event featured keynotes, panel discussions, and breakout sessions focused on AI security, software supply chain governance, and policy recommendations for secure OSS consumption.
“The OpenSSF is committed to tackling the most pressing security challenges facing the consumption of open source software in critical infrastructure and beyond ” said Steve Fernandez, General Manager, OpenSSF.
Discussions highlighted the importance of industry-led security initiatives, collaboration with policymakers, and the need for standardized security frameworks. Following the summit, OpenSSF will refine security guidance and best practices to enhance open source software security globally. Learn more about the event, key takeaways, OpenSSF’s Vision, and how to get involved in shaping open source security policy.

The OpenSSF and Linux Foundation Education have launched a new, free cybersecurity e-Learning course, Security for Software Development Managers (LFD125). Designed for those who manage or aspire to manage developer teams, this course covers critical security concepts needed to build resilient applications. Participants will learn how to identify vulnerabilities, implement proactive security measures, and guide their teams in creating secure software. Security for Software Development Managers (LFD125) is a self-paced, 2-hour course that includes access to a discussion forum for engagement with experts and peers. Upon successful completion, participants receive a digital badge and certificate.
Enroll today and strengthen your leadership skills in software security!
You’re invited to…
We want to get you the information you most want to see in your inbox. Have ideas or suggestions for next month’s newsletter about the OpenSSF? Let us know at marketing@openssf.org, and see you next month!
Regards,
The OpenSSF Team
In this inspiring episode of “What’s in the SOSS?”, we welcome our new Co-Host, cybersecurity expert and open source advocate Yesenia Yser. Join hosts CRob and Yesenia as they delve into her compelling journey from discovering open source at Red Hat to pioneering AI security at Microsoft. Learn how Yesenia blends her passion for cybersecurity, Brazilian jiu-jitsu, and empowering communities—especially women—to shape her personal brand and advocacy efforts. Don’t miss this lively conversation full of actionable insights for anyone interested in cybersecurity, open source communities, and personal growth.
00:18 – Introduction to Yesenia Yser
00:55 – Yesenia’s open source origin story
03:30 – From cybersecurity professional to jiu-jitsu practitioner
05:56 – Building a personal brand in tech and beyond
09:04 – Advocating diversity in tech through the BEAR group
12:40 – Fun rapid-fire round (VI or Emacs, Coke or Pepsi, favorite open source mascot, spicy vs. mild food, and more)
13:52 – Yesenia joins as new co-host of “What’s in the SOSS?”
15:39 – Advice for breaking into open source and cybersecurity
Soundbite – Yesenia Yser
One thing that you’ll hear me advocate over and over again is to find an open source project that will support your career growth. Whether you’re looking to go into program management, business analyst, management, or your technical skills, find a project that aligns with you. You can jump on the open source Slack and hit up in general, just say, I’m interested in doing this, this, this. This is how many hours I have. And I bet you someone’s going to be.
Hey, come over to our group, join us. We’ll teach you along the way. That’s the best thing I know about open source and the tech is that folks are very open to teach.
Intro – CRob (00:18)
Hello and Welcome to “What’s in the SOSS?” OpenSSF’s podcast where we talk to interesting people throughout the open source ecosystem. My name is CRob, one of your hosts, and today we have an incredible treat. I’m talking to a very dear friend of mine and amazing open source contributor, Yesenia. We have some amazing news to share at the end of the podcast today.
CRob (00:49):
Yesi, please introduce yourself to the audience and tell us about your open source origin story.
Yesenia Yser (00:54):
Hey everyone! Thank you for those listening. I’m Yesenia, born and raised in Miami, South Florida. I’m Cuban American, I’ve been in the cyber tech industry for over 12 years, a bachelor’s in computer science, and a master’s in digital forensics. I usually like to joke that I “social engineered” my way into my first security role. It was always interesting because in school I used a bunch of tools that were online and free.
My first couple of jobs, we used a bunch of libraries and things of that nature. It wasn’t until my time at Red Hat, which was like six years into my career that I realized what I was actually using and that it was open source and there was a huge community of great and amazing folks behind it that are part of it. So from there, I started exploring open source more exploring OpenSSF, a community that I do a lot of, advocacy work and contribution to. But it was just, it was very interesting that for someone that uses it, this is just, you know, everyday person that’s like learning how to code. You bring in Python, you import your libraries and you got to keep them up to date every now and then. And you don’t really know where they come from, but they come from a little black hole that’s called the open source space. Then, my journey took me from Red Hat. worked at the Linux foundation on the Alpha-Omega project. So I was helping with the Omega piece of it and we, in which we were automating, security vulnerability identification and open source software. Then my career took me to Microsoft where right now I’m working on artificial intelligence and open source security research. In that space, I get to explore both AI from the large tech industry and all the threats and yumminess that is in this emerging new technology. And then I get to share my love and passion for open source.
CRob (02:48):
That’s awesome. And as we mentioned, you and I both work together at Red Hat, where you were the very first supply chain security engineer. So I am a little bit more up to speed with your background than other folks may be. But, I think what I find very fascinating about you is that you not only are an amazing technologist and super smart, but you also have a lot of outside of work activities that I find very fascinating. Could you maybe talk about how things like your passion for jiu-jitsu and outside activities kind of inform your practice around open source security and AI security?
Yesenia (03:30):
Yeah. So starting at Red Hat was pretty, pretty cool. I was there as the first supply chain security engineer. A very big breach happened called SolarWinds, in which it blew up the supply chain security space for the industry. So, it was really great to be in the forefront of that in such a big company that is big and open source and be able to see all the plethora of things that happened in the wild wild west that is the development industry.
So outside of work is usually what I like to say about my day job. So by the day, I’m a security professional. By night, I’m a jiujiteira, which means a jiu-jitsu practitioner. I’ve been working, I’ve been training and teaching jiu-jitsu for almost seven years now. Started with the kids and working with them. And it was just lovely to see their faces bright light up when they learned a new technique. And over the years I’ve seen parallels between jiu-jitsu and my own cyber career, in which I became a mirror of things that I was seen as myself in a leader in the cyberspace that was holding me back. And then that was being mirrored into my jiu-jitsu. A year or so ago, I started a nonprofit called the Lioness Instincts, in which our mission is to empower women to protect themselves both physically and digitally, because as a security professional and a presented to jiu-jitsu instructor, which we would teach women’s self-defense classes and teach kids. I saw a huge boost in just their self-confidence and being able to work through some of the traumas that does happen through some of the crazy things that happen throughout the world. So we started the nonprofit. And if I’m not in the cyber world, I’m on the mat teaching and training. I also have two dogs that I teach and you’ll see me with them as well.
They’re their own plethora of tricks and cuteness.
CRob (05:25):
That’s awesome. And I know how much this kind of outside advocacy and your jiu-jitsu kind of affects, know, it colors your thinking and how you conduct yourself. Let’s think about this. I know you’ve kind of taken this and kind of started to develop a personal brand around these types of things. Can you maybe say why it’s important for people to find these opportunities and these passions and kind of try to do this for themselves? How does this personal branding help you?
Yesenia (05:56):
Yes. So for me, it’s my personal brand. And for those that follow, I’m called cyber jiujiteira online because of the mixture of, me, gives me a purpose and an avenue. And usually when I make a decision of something that I’m going to do, I ask myself, does it match or fit my brand? And my brand has its own pillars of advocacy as it has its five, has its five pillars, which is, cybersecurity and promoting advocacy, education and guidance to get more folks into the industry. There’s just the empowerment, self-defense, digital privacy piece that involves digital and the physical side, teaching and lessons, motivation, and then lifestyles. Because I normally talk to folks and they’re like, you have a very interesting lifestyle of just working in training, working in training, and then running a nonprofit. So I feel like a brand helps you not only keep because I have ADHD, so I’m all over the place, but it helps me keep aligned with what I’m doing and then ensuring that I can go back to it when it comes to social media platforms, it helps people know who I am and what I stand for. So I’ve been in conferences, both physical, like for jiu-jitsu things, and then for cybersecurity things or open source. And they’re like, you’re the jiu-jitsu girl. You’re the cyber girl. So it’s great. I’m like, yeah, you know me.
It becomes a cool way for folks to connect with you on a more personal level, and understand who you are. And in that, once you hear that you understand that I’m a martial artist and any thoughts around martial artists, you relate it to me in a, in a way. So martial artists tend to be disciplined. They tend to be focused. They tend to have patience. So as an individual that’s applying to cybersecurity roles that are fast pacing, working with executives. Things are constantly moving. You have to adapt quickly. The mindset of a martial artist, I think, falls very well into that, which helps with interviewing. And somebody said it the other day, which I think is great for branding, is your brand should be getting you the interviews. So instead of you searching out for these interviews, your brand should be helping you acquire what’s right for you.
And it’s just very important when you’re networking and connecting with folks that your brand speaks on who you are, whether or not you’re in the room.
CRob (08:29):
Excellent. Yeah. And thank you for all you do for especially, you know, late getting ladies into cyber and talking about self-defense. I think that’s amazing contribution back given back. We get to work together in the open SSF as part of a group that also has a lot of very strong advocacy bent to it. So maybe could you talk a little bit about the bear group that we participate in and you know, why is it so important to kind of bring awareness and kind of reach out to people that may not be currently in this career path of this world.
Yesenia (09:03):
Yes. So the BEAR, I think what we’re doing in the group is great. So bear stands for belonging.The E is empowerment, is for allyship and R is for representation. And I, I strongly feel very passionate about this because in the open source space, let’s just start with the challenges. A lot of the times are open source maintainers. They created this when they were younger. It was a college project. It was just a fun idea that they had and somehow it went very mainstream. It went viral, blew up, and now is in 80 to 90 % of software that’s out there, right? So we have this one tool that’s maintained by one person who probably has a family, who probably works two or three jobs. And it’s crucial to everything from US government infrastructure to maybe you know, outside sources to big tech company, industries. So the idea of Bayer is to be able to make that bridge a little bit easier for folks. Cause I know myself when I was starting, as I mentioned earlier, I didn’t know what open source was. was just like, okay, some cool thing that I can pull from online, but having these like community office hours, which we do once a month, we get to highlight different areas of like how to get started into space, how to look for mentorships.
We talk about your branding and how to get that. And we just highlight a lot of amazing voices in the community and that we are associated with to bring out different representations and ideas that will help folks understand how to get into the industry. This is also for folks already in the industry, because if you want to give back or you have knowledge that’s very important, you can set up your own mentorship. You can join our community and plan different events.
We’re looking to also host conversations at different OpenSSF and open source community conferences. And this advocacy is important because it’s going to give maintainers and open source contributors a little bit of extra break room to bring more folks in. One of the biggest issues you hear is that people just don’t have time. But if they have an individual…it’s willing to take on a task, right? And it doesn’t have to be a coding task. It can be writing documentation to make it easier for other people to use it. It could be updating the website. It could be a plethora of different skills that doesn’t require coding that can assist the maintainer in coming on. And we can just improve our open source software and tools usage.
CRob (11:43):
Yeah, it’s an, love the mission of the bear group and I love kind of the, how we’re moving forward with the community office hours. I think it’s been really impactful to kind of give these different perspectives and try to help have a very broad contributor base and help people break into something that sometimes there’s a lot of obstacles to, right?
Yesenia (12:04):
There’s a lot. And if you’ve missed any of the previous ones, they’re on YouTube. You can check them out and join us on Slack and ask, know, questions. We’ll be willing to either make a community office hours specific for that or just answer your questions right there on Slack. Even if you’re looking for a project.
CRob (12:23):
Cool. Well, let’s move on to the rapid fire part of the interview. All right. I have a couple of wacky questions. You probably don’t want to be drinking a drink when I ask you this. We don’t need any spit takes, but first question, VI or Emacs.
Yesenia (12:42):
VI or Emacs, we’re going to go with VI.
CRob (12:45):
Nice. Excellent, excellent. There are no wrong answers.
Yesenia (12:49):
Here. Haha.
CRob (12:52):
Next question, Coke or Pepsi? Yes, there was a right answer for that one and you’ve got it. Who’s your favorite open source mascot?
Yesenia (12:54):
CRob with the goose hat.
CRob (13:05):
CRob the goose hat?! Haha.
I don’t think you have a tattoo of that one yet though.
Yesenia (13:11):
Yet, but the one I do have a tattoo is Tux
CRob (13:15):
Very nice. What’s your favorite adult beverage?
Yesenia (13:19):
Coffee. This place is coffee.
CRob (13:23):
Yum yum yum. Love me some coffee. And last rapid fire question, spicy or mild food?
Yesenia (13:31):
None of the above. I’m Cuban. We don’t do spicy. It all hurts. haha.
CRob (13:39):
Fair enough.
Yesenia (13:40):
Seasoned, seasoned with a dull.
CRob (13:43):
Okay, excellent.
Well, thank you for playing rapid fire. So before I move on to our last question, I wanted to let the audience know that Yacinia is going to be joining us as a featured co-host of What’s in the SOSS. So you’re going to see her talking to some other amazing, interesting people. Do you want to give us kind of a little taste of what you, kind of the types of topics or people you’re interested in exploring as you’re going through and doing interviews?
Yesenia (14:11):
Yeah, I’m just interested in getting folks in the open source community and then external that may not even be aware that they’re using open source or how they can get involved. Our upcoming community office hours is going to bring in some amazing voices. But really just anybody that’s interested in speaking, speaking in the open source, talking about their journey in any shape or form or bringing in some technical coolness that, you know, like to spice up the SOSS, right?
So if you are interested… Was that the play if I said spicy? Yeah, I had feeling that was going be the audio.
Yeah, just looking at my list, but, once I post, this episode or just a general call for action, I’ll keep the community up to date, but if anyone listening to this is interested or has an awesome voice that they would love to share the space with, let me know.
CRob (15:11):
Yeah, I think this is going to be really amazing. Kind of reaching out to new voices and perspectives and just kind of broadening the awareness of the things the foundation does and the importance of open source security. So thank you for joining us. Yeah. And to that end, as we launch you off on your new endeavor, what’s your call to action or what advice do you have for people trying to get into this crazy field of cyber and open source security?
Yesenia (15:24):
Thank you for having me.
One thing that you’ll hear me advocate over and over again is to find an open source project that will support your career growth. Whether you’re looking to go into program management, business analyst, management, or your technical skills, find a project that aligns with you. You can jump on the open source Slack and hit up in general, just say, I’m interested in doing this, this, this. This is how many hours I have. And I bet you someone’s going to be.
Hey, come over to our group, join us. We’ll teach you along the way. That’s the best thing I know about open source and the tech is folks are very open to teach.
CRob (16:18):
Well, again, thank you for joining us today and thank you for volunteering to help us co-host the podcast. And we look forward with eager anticipation to the amazing interviews you’re going to do for us. And with that, it’s a wrap. Thank you all for joining us today.
Yesenia (16:29):
It’s going to be amazing. Thank you.
CRob (16:38):
Thank you.
Outro (18:40):
Enjoyed the podcast? Subscribe to “What’s in the SOSS?” on Spotify, Apple Podcasts, Pocket Casts, or your favorite platform. Stay updated with OpenSSF news and events by subscribing to our newsletter at openssf.org/newsletter. Join the OpenSSF community at openssf.org/get-involved, and connect with us on LinkedIn.
Thanks for listening, and we’ll catch you next time on “What’s in the SOSS?”


The OpenSSF Policy Summit DC 2025 brought together open source, government, and industry leaders to tackle pressing security challenges. The event fostered open dialogue under the Chatham House Rule, emphasizing shared responsibility and commitment to strengthening the open source ecosystem.
“The OpenSSF is committed to tackling the most pressing security challenges facing the consumption of open source software in critical infrastructure and beyond. Our recent Policy Summit highlighted the shared responsibility, common goals, and commitment to strengthening the resilience of the open source ecosystem by bringing together the open source community, government, and industry leaders.” – Steve Fernandez, General Manager, OpenSSF
The summit opened with remarks from OpenSSF General Manager Steve Fernandez emphasizing the importance of collaboration between industry, government, and the broader open source community to tackle security challenges. Jim Zemlin, Executive Director of The Linux Foundation, delivered a keynote on the importance of securing open source in modern infrastructure, followed by Robin Bender Ginn of the OpenJS Foundation, who provided insights into systemic security challenges. Panels covered key topics such as integrating security into the software lifecycle, regulatory harmonization, AI security risks, and the adoption of open source in government.
The policy summit included various breakout sessions; below are some key takeaways from each.
AI security is at a crossroads, with many of the same supply chain risks seen in traditional software. Unlike past security crises, AI has not yet had its “Heartbleed moment”, making this the time to proactively address risks.
AI presents both new challenges and an urgent need to reinforce existing security efforts led by OpenSSF and The Linux Foundation. If the origins of AI models are unclear, how can we truly trust them? Understanding and measuring the risks associated with AI is critical, especially as AI frameworks and libraries integrate with other tools, potentially introducing new vulnerabilities. Yet, security in this space is often left as an afterthought—an exercise for the user rather than a built-in safeguard. As AI intersects with open source software, traditional cybersecurity risks remain relevant, raising key questions: What are the existing guardrails, and how can we strengthen them to ensure a more secure AI ecosystem?
The conversation centered on improving how open source components are updated, ensuring clear maintenance statuses, and reducing dependencies on U.S.centric platforms.
Improving component updates is a critical challenge, especially when backward-incompatible changes prevent seamless upgrades. The industry needs clear guidance on enabling and streamlining updates, ensuring that software remains secure without unnecessary friction. Best practices for downstream consumers should be more widely established—such as evaluating whether a project is actively maintained before adopting it and identifying major backward-incompatible API changes as potential risks.
A structured approach to declaring an open source project’s maintenance or production status is also essential. There should be a formal, machine-ready way to indicate when a project is no longer maintained, making it easy to see and act upon. Additionally, as organizations strive to avoid being U.S.centric, requirements should be designed to be platform-agnostic rather than tied to specific tools.
Transparency is another key consideration. There needs to be a way to self-attest disagreements in security scans—allowing individuals to provide justification with supporting URLs when a requirement is met or missed. While knowing who maintainers are can be useful, it should not be the sole security measure.
Finally, ensuring that executables match their claimed source code is fundamental to software integrity. Protecting the build process through frameworks like SLSA and enabling verified reproducible builds can help mitigate risks, preventing attacks like those seen with xz utils.
As open source software faces increasing regulatory scrutiny, the need for cross-compliance agreements and clear policies has become a priority.
There are many open questions surrounding the EU’s Cyber Resilience Act (CRA)s definition of an open source steward. Clarity on what qualifies as stewardship is essential, as it impacts compliance responsibilities and obligations under the regulation.
A key concern for organizations navigating the CRA is the lack of a Mutual Recognition Agreement (MRA)—a framework that would allow compliance with one regulation to satisfy the requirements of another. Without this reciprocity, manufacturers must meet CRA standards separately to sell in Europe, adding complexity for global companies. Many U.S.based organizations are now grappling with whether and how to align these requirements domestically to avoid maintaining multiple sets of policies.
One proposal to strengthen open source sustainability is requiring government contracts to include provisions mandating that any changes to open source software made as part of the contract be contributed upstream. This would ensure that improvements benefit the broader ecosystem rather than remaining siloed.
Another growing concern is the financial sustainability of open source projects. Large organizations often look to cut costs, and open source funding is frequently among the first areas to be reduced. Regulation could help prevent this by recognizing the critical role open source plays in security and innovation.
Finally, organizations need better ways to quantify the impact of their open source contributions across distributed teams and departments. Some efforts are underway to address this challenge, but it remains difficult to track how contributions tie back to business value. While The Linux Foundation’s LFX provides some insight, similar visibility is lacking across other foundations, leaving a gap in industry-wide solutions.
Discussions focused on improving how package repositories handle security and lifecycle management.
The group explored how to effectively track when open source projects reach end-of-life or end-of-support, recognizing the need for clearer visibility into project status. One proposal discussed was the Global Cyber Policy Working Group’s idea to introduce a “steward.md” file, which would explicitly indicate whether a project is maintained by an OSS Steward. A key question raised was how package repositories should track and surface Steward information. Ensuring that repositories can reliably display this data would help users make informed decisions about software adoption and maintenance. Security was another focus of discussion, particularly the importance of isolating components of the build pipeline to minimize attack surfaces. One suggestion was to remove pre-install scripts, which can introduce vulnerabilities if not properly managed. Finally, the group considered next steps for the Principles of Package Repository Security document. Identifying priority areas for improvement will be crucial in strengthening repository security and ensuring alignment with broader security best practices.
The Policy Summit reinforced OpenSSF’s commitment to improving open source security through collaboration and actionable insights. We encourage the community to stay engaged and contribute to ongoing efforts in these key areas.