
By Eddie Knight, Sonatype
Let’s get it out of the way early: it’s not always clear how you can best plug into organizations like OpenSSF. That’s why I’m writing this guest blog post as an “outsider.” I’m just your average tech employee who has become progressively more involved since my company, Sonatype, became members of OpenSSF.
Most recently, I was able to lead a booth for OpenSSF at Devnexus, the largest Java conference in North America.
The booth opportunity would have been a stretch, except for the fact that Lori Lorusso had arranged an introduction for Devnexus to collaborate with OpenSSF. After introductions were made, the only thing left was for the OpenSSF staff to find someone who was available to travel to Atlanta to run the booth.
I was scheduled to be speaking at the event already, excited to share about the research I had done recently with Theresa Mammarella to create an impact analysis of different security testing methodologies. Actually, I created a short writeup of our findings for you to read.
Being scheduled to speak, I normally would also be helping out at the Sonatype booth, talking to folks about things like SBOMs, and how enterprises use our tools to secure their open source consumption. But I was lucky to get approval from my leadership to step away and spend the entire event at the OpenSSF booth talking about this cross-industry collaboration to secure open source software across the board. Fortunately, my big boss Brian Fox is on the board of OpenSSF and has a strong belief in the vision and mission of this organization!
Once I got the booth set up, with a couple banners behind me and a massive pile of candy on the table, the only thing left was to make sure I had a plan for how to talk about OpenSSF once people showed up. As it turns out, I got better at explaining things the more I talked about all the cool stuff OpenSSF is doing and how I’ve engaged.
A few different things helped me solidify my language.
Did you know that the Cloud Native Computing Foundation (CNCF) uses the OpenSSF Scorecard as part of their security measurement tooling, CLOMonitor? In that way, OpenSSF became a critical contributor to the security overhauls done during last year’s Cloud Native Security Slam (and likely will be again this fall).
Did you know that the same Scorecard tooling is a core part of Sonatype’s machine learning algorithms that are able to get an 89% accuracy when predicting the presence of an un-reported vulnerability in open source tooling. In that way, the Scorecard has directly contributed to our ability to find threats and protect our users!
Okay last example, before I get carried away. Did you know that OpenSSF’s Alpha-Omega project is not only working on technical solutions, but is also financially supporting other open source foundations to ensure secure development of the most critical open source projects? For example, OpenSSF has recently announced that they were able to help the Python Software Foundation hire a security engineer in residence.
As it turns out, these types of examples were really handy for helping people quickly understand the general vision of OpenSSF (while standing at a booth holding bags full of swag from days full of visiting conference booths).
But all of this is just my most recent experience.
How I first got involved (and so can you!)
It wasn’t an extremely complex journey for me to get involved with OpenSSF, but it can be a bit overwhelming when you’re first getting connected.
First, there is a lot going on– all working toward the same general set of goals. In that way, OpenSSF is different from a lot of other open source foundations that primarily host software projects with a diverse range of use cases.
The Apache Software Foundation hosts more than 200 independent software projects that solve a diverse problem set. The Fintech Open Source Foundation hosts diverse projects with a shared vision: “software and standards that address common [financial services] industry challenges and drive innovation.” Meanwhile, OpenSSF has a wide array of groups and projects that work “both upstream and with existing communities to advance open source security for all.” In practice, it becomes hard to get involved with any one project and not impact or be influenced by other projects.
In practice, there are quite a few meetings happening every week to move a different part of the vision forward, and more that meet monthly or bi-weekly.
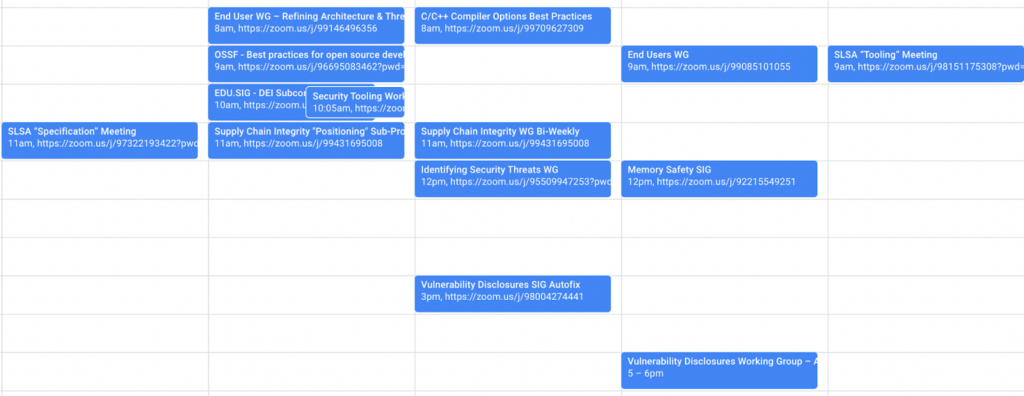
Because Sonatype specializes in providing enterprise supply chain security, we have folks active in a variety of efforts, including the Education SIG, End Users WG, Best Practices WG, Security Scorecard, and Sigstore. Drawing on information from my colleagues, I have been able to find the best places to connect and get involved in a productive way.
If you’re connecting for your first time, the recommended engagement path is effectively “choose your adventure!”
Take a look at the existing OpenSSF materials to learn more about the organization and its offerings, then take a look at the list of working groups and then check the community calendar to find a meeting that you think will be a good starting point. When you join a call for the first time, just introduce yourself as a newcomer and share your goals with the group. This is very much a community effort, so you’ll likely get some good advice from anyone you speak to on an official call (and if not, try again with a different group).
Also, don’t forget to join the OpenSSF Slack, where you can asynchronously reach out with any questions, or just join the channels you’re interested in to watch and learn more about what’s happening.
I look forward to seeing you around!