By Raghav Kaul (Google), Jonathan Howard (Lockheed Martin), Keith Ganger (Lockheed Martin), Jim Robison (Lockheed Martin), Sam White (GitLab), Derek Ferguson (GitLab)
Introduction
Today, we are excited to announce OpenSSF Scorecard v4.12. This release adds support for GitLab and brings the project closer to its longer-term goal of supporting all types of hosted repositories. Previously, Scorecard has been limited to GitHub-based repositories along with some support for local Git repositories.
OpenSSF Scorecard Recap
Scorecard helps both developers and open source consumers to determine how well an open source project follows best practices. Think of it like a good restaurant review – when a developer wants to add a new software dependency to their project, Scorecard provides data and checks that allow a developer to assess, “do I want to use this library?”, equivalent to “do I want to eat here?” By gathering evidence of software best practices, Scorecard helps paint a picture of how seriously a project takes its security. Scorecard assesses projects on dimensions such as whether the project is consistently maintained, whether the project pins its dependencies, and whether the project’s code undergoes code review before merge.
State of Open Source on GitLab
Today, GitLab is hosting an ever-growing number of open source projects and provides full support for those projects. Within our goal of meeting developers where they are today, it’s imperative that Scorecard continues to expand wherever developers are working. Starting with this release, OpenSSF Scorecard will be scanning over 28K projects hosted on GitLab and make it possible to run within a CI pipeline.
Getting Started
You can run Scorecard today on a GitLab.com (or self-hosted GitLab) repository by running Scorecard as you normally would:
scorecard --repo gitlab.com/<org>/<project>/<subproject>To give Scorecard more accurate data, you can create a GitLab Access Token, set the GITLAB_AUTH_TOKEN environment variable, and run Scorecard as you normally would:
export GITLAB_AUTH_TOKEN=glpat-xxxx
scorecard --repo gitlab.com/<org>/<project>/<subproject>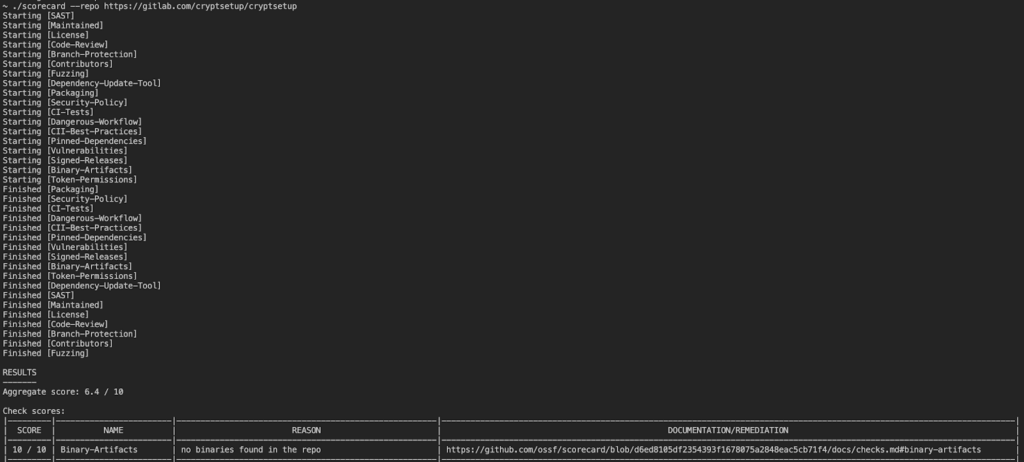
Fig 1. Running Scorecard on a GitLab repo
You can also run a specific check on a GitLab repo, like the Code-Review, which checks how often a project reviews and approves code before merge.
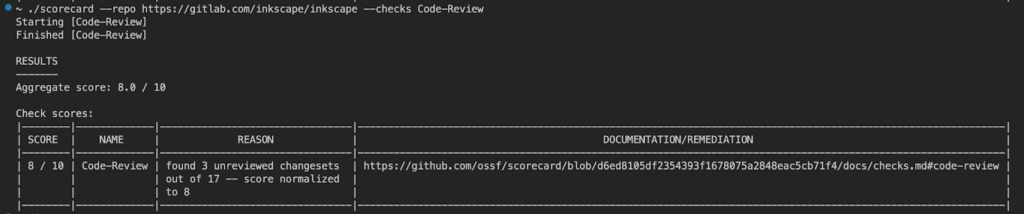
Fig 2. Running Code-Review on a GitLab repo
Scorecard scores for GitLab repositories are also visible in deps.dev (e.g. baserow/baserow), as well as in Scorecard’s public BigQuery dataset. To see how to access Scorecard’s BigQuery data, see the project documentation. Finally, to continually monitor your project’s score for changes, and to catch repository security misconfigurations with Scorecard, you can also run Scorecard automatically in your GitLab project’s CI/CD (see the sample code).
What’s Next
We’re always looking for ways to improve Scorecard and add support for new ecosystems, package managers, and security checks. If you are interested in contributing support for Scorecard’s GitLab integration or adding support for another source code management (SCM) system to Scorecard, please contribute!
Special Thanks
A few contributors helped to make Scorecard v4.12 happen. Special thanks to: jhoward-lm, kgangerlm, jimrobison, raghavkaul, spencerschrock, and N8Bwert.
About the Authors
Raghav Kaul is a Software Engineer on the Google Open Source Security Team working on Scorecard and Allstar.
Jonathan Howard is a Full Stack Engineer with Lockheed Martin, primarily working as a developer on the Hoppr project and the Hoppr OpenSSF Scorecard plugin.
 Keith Ganger is a Product Architect with Lockeheed Martin currently focused on Enterprise Supply Chain Security and DevSecOps.
Keith Ganger is a Product Architect with Lockeheed Martin currently focused on Enterprise Supply Chain Security and DevSecOps.
 Jim Robison is a Full Stack Engineer Sr Stf with Lockheed Martin. He has more than 20 years experience in application development, with a current emphasis on kubernetes, and cloud migrations.
Jim Robison is a Full Stack Engineer Sr Stf with Lockheed Martin. He has more than 20 years experience in application development, with a current emphasis on kubernetes, and cloud migrations.
 Sam White is a Group Manager, Product at GitLab focused on Software Supply Chain Security. He has experience in a wide range of areas within security including security scanning, runtime security, endpoint security, and automatic signing. He has a passion for making it easy for developers to build secure products by enabling secure features by default.
Sam White is a Group Manager, Product at GitLab focused on Software Supply Chain Security. He has experience in a wide range of areas within security including security scanning, runtime security, endpoint security, and automatic signing. He has a passion for making it easy for developers to build secure products by enabling secure features by default.
 Derek Ferguson is a Group Manager, Product at GitLab. Having worked in security and performance testing for over 10 years and application development for 20 years, he is passionate about integrating security-conscious practices and proactive testing into the development lifecycle as early as possible. His focus is on enabling developers to manage, secure, and test their own code.
Derek Ferguson is a Group Manager, Product at GitLab. Having worked in security and performance testing for over 10 years and application development for 20 years, he is passionate about integrating security-conscious practices and proactive testing into the development lifecycle as early as possible. His focus is on enabling developers to manage, secure, and test their own code.