OpenSSF Notes Quarter of Growth with New Members, Added AI Security Resources, and Growing Community
Foundation celebrates five additional members, new cyber reasoning sandbox project, and release of v1.0.0 Python Secure Coding Guide to support open source security globally
MINNEAPOLIS – OpenSSF Community Day North America – May 21, 2026 – The Open Source Security Foundation (OpenSSF), a cross-industry initiative of the Linux Foundation focused on sustainably securing open source software, today announced five new members have joined the foundation. The OpenSSF also notes additional technical resources for Python secure coding, the first cohort of OpenSSF Ambassadors, and new projects like OSS-CRS joining the foundation’s sandbox during OpenSSF Community Day North America in Minneapolis. OpenSSF’s efforts ensure that open source remains a trusted foundation for digital innovation by addressing the technical, legal, and human elements of modern cybersecurity.
These milestones address two main converging pressures in the software ecosystem: increasingly mandatory security standards and the need to unify organizations and countries behind those standards. By providing practical resources, the OpenSSF helps projects navigate complex requirements such as the CRA. The project continues to expand its global community as well, keeping all that benefit from open source software ahead of sophisticated risks and threats.
“As the threat landscape for software supply chains becomes more complex, the need for community driven security standards has never been more urgent,” said Steve Fernandez, General Manager of OpenSSF. “The growth we’re seeing in our membership and the arrival of projects like OSS-CRS show that security is an important priority for all. The OpenSSF is providing the practical tools and guidance developers need to build more resilient software.”
New OpenSSF members include ActiveState, Aikido, Minimus, and TuxCare, who join the Foundation as General Members. The FreeBSD Foundation also joins as an Associate Member. These organizations will contribute to working groups and technical initiatives to help drive the strategic direction of the OpenSSF. By collaborating within a neutral forum, these members support the long term sustainability of the open source ecosystem.
Foundation Updates and Milestones
In the second quarter of 2026, the OpenSSF achieved several milestones to secure and support more resilient software for all:
- Publication of the European Union Cyber Resilience Act (CRA) Guides and Resources for Maintainers and Stewards: The Global Cyber Policy Working Group created this technical roadmap to help foundations and projects navigate global regulations, including the EU Cyber Resilience Act (CRA).
- OSS-CRS Joins OpenSSF: Following its debut in the DARPA AI Cyber Challenge, the Open Source Cyber Reasoning System (OSS-CRS) has been formally accepted as an OpenSSF Sandbox project to advance AI-driven automated vulnerability finding and patching.
- First Release of the Python Secure Coding Guide: The BEST Working Group has announced version 1.0.0 release of the Secure Coding Guide for Python, providing developers with high-confidence anti-patterns and compliant code examples to mitigate common vulnerabilities.
- Security Slam 2026 Conclusion: OpenSSF celebrates the successful completion of Security Slam 2026, which resulted in dozens of open source projects reaching the Open Source Project Security (OSPS) Baseline and publishing their first formal threat models.
- New AI Security eBook: In collaboration with the Cloud Native Computing Foundation (CNCF), OpenSSF released Securing Open Source in the Age of AI: A Practical Guide for Maintainers, Security Engineers, and Researchers. The guide offers actionable advice for managing AI generated contributions and using AI to improve security.
- Mentorship Program Expansion: OpenSSF selected eight mentees for its Summer 2026 program. These contributors will provide dedicated support to Repository Service for TUF (RSTUF), GITTUF, SBOMit, and Minder.
- Inaugural Ambassador Program Cohort: Today at OpenSSF Community Day, the Foundation announced the first cohort of the OpenSSF Ambassador Program, featuring 13 community leaders dedicated to spreading security best practices.
Supporting Quotes
“The Linux Foundation and OpenSSF are where the serious work on open source security gets done. No single organization secures the software supply chain alone. Thirty years of building secure open source infrastructure is what we bring to that work, and that work is better done together.”
– Abby Kearns, CEO, ActiveState
“Open source software is the foundation of modern software development, and supporting that ecosystem has always been core to Aikido’s mission. Through projects like Safe Chain, Zen Firewall, OpenGrep, and BetterLeaks, we’re investing in practical, community-driven security tooling that helps developers build and ship software with speed, trust and confidence. We believe securing open source is a shared responsibility, and we’re proud to contribute technologies that make the broader ecosystem safer and more resilient for everyone.”
– Willem Delbare, Founder and CEO, Aikido Security
“As a critical component of the global digital infrastructure, we believe FreeBSD must be part of the security discussions shaping the future of open source. Joining the OpenSSF will enable us to collaborate with others to help protect the software the world depends on.”
– Deb Goodkin, Executive Director, FreeBSD Foundation
“Minimus is proud to join OpenSSF and work alongside its other members to help secure the open source ecosystem that allows us all to thrive. Enabling developers to build on open source components while keeping security teams happy is central to our business, and we intimately understand the responsibility we all share in achieving that goal.”
– Kat Cosgrove, Head of Developer Advocacy, Minimus
“TuxCare is pleased to be joining OpenSSF and the cross-industry effort to strengthen open-source security. For more than a decade, we’ve worked to keep open source secure and reliable in enterprise production over the long term. We see that kind of sustained reliability as essential to the trusted, secure open-source ecosystem OpenSSF envisions.”
– Igor Seletskiy, CEO, TuxCare
Events and Gatherings
OpenSSF members are gathering this week in Minneapolis at OpenSSF Community Day North America. To get involved with the OpenSSF community, join us at the following upcoming events: OpenSSF Community Day Europe (Prague; October 6) and Open Source Summit Europe (Prague; October 7-9).
Additional Resources
- View the complete list of OpenSSF members
- Contribute efforts to one or more of the active OpenSSF working groups and projects
- Sign up for the OpenSSF newsletter to receive updates on upcoming events, resources, and community news.
About the OpenSSF
The Open Source Security Foundation (OpenSSF) is a cross-industry organization at the Linux Foundation that brings together the industry’s most important open source security initiatives and the individuals and companies that support them. The OpenSSF is committed to collaboration and working both upstream and with existing communities to advance open source security for all. For more information, please visit us at openssf.org.
About the Linux Foundation
The Linux Foundation is the world’s leading home for collaboration on open source software, hardware, standards, and data. Linux Foundation projects are critical to the world’s infrastructure, including Linux, Kubernetes, LF Decentralized Trust, Node.js, ONAP, OpenChain, OpenSSF, PyTorch, RISC-V, SPDX, Zephyr, and more. The Linux Foundation focuses on leveraging best practices and addressing the needs of contributors, users, and solution providers to create sustainable models for open collaboration. For more information, please visit us at linuxfoundation.org.
The Linux Foundation has registered trademarks and uses trademarks. For a list of trademarks of The Linux Foundation, please see its trademark usage page: www.linuxfoundation.org/trademark-usage. Linux is a registered trademark of Linus Torvalds.
Media Contact
Grace Lucier
The Linux Foundation
pr@linuxfoundation.org

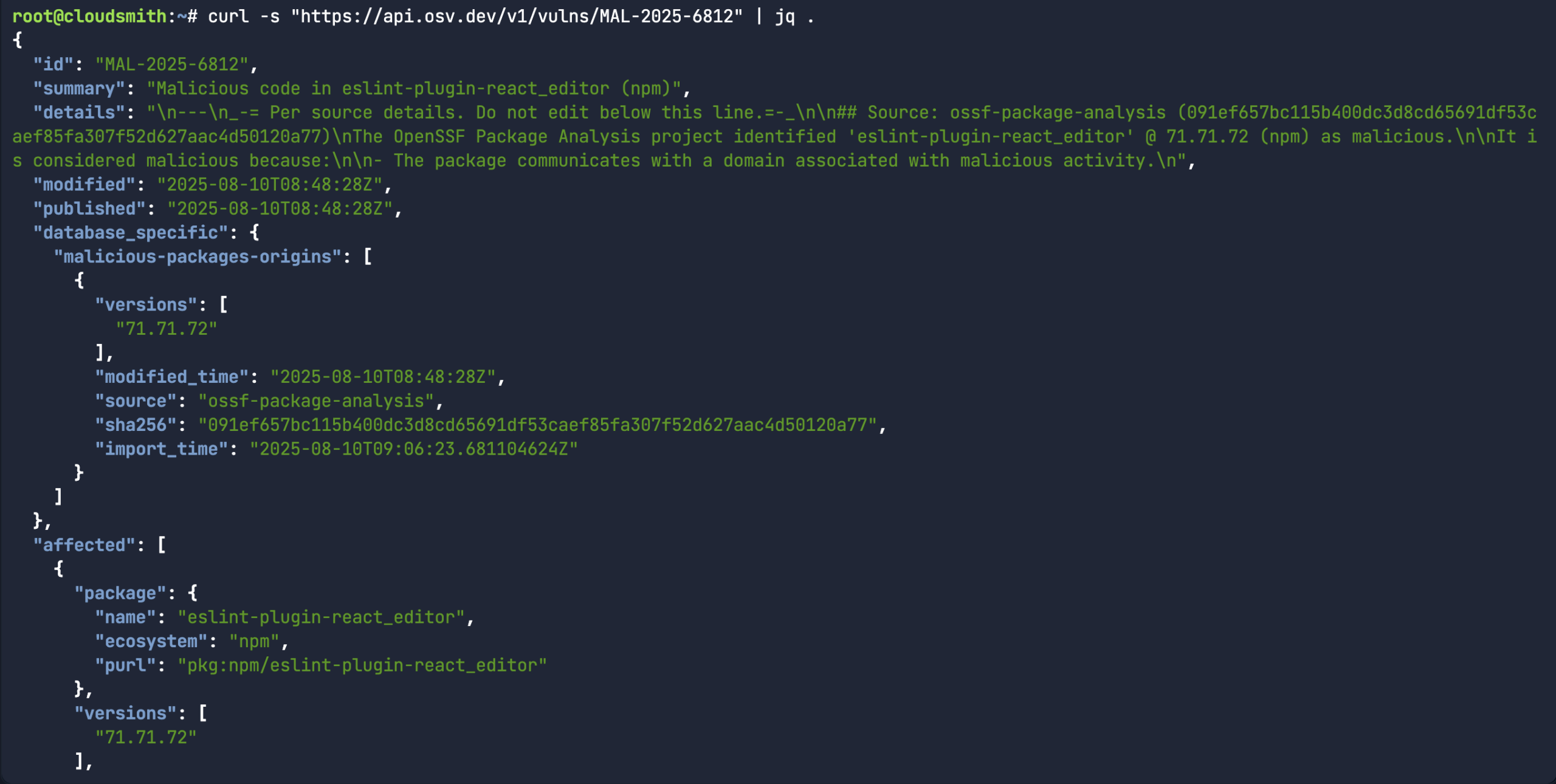 While the above command does return a bunch of information about a specific malicious package record, it would assume you already knew what the malicious package ID was in the first place. A more common use-case for the API is to look for a specific package name/version and the associated open source upstream source (ie:
While the above command does return a bunch of information about a specific malicious package record, it would assume you already knew what the malicious package ID was in the first place. A more common use-case for the API is to look for a specific package name/version and the associated open source upstream source (ie: 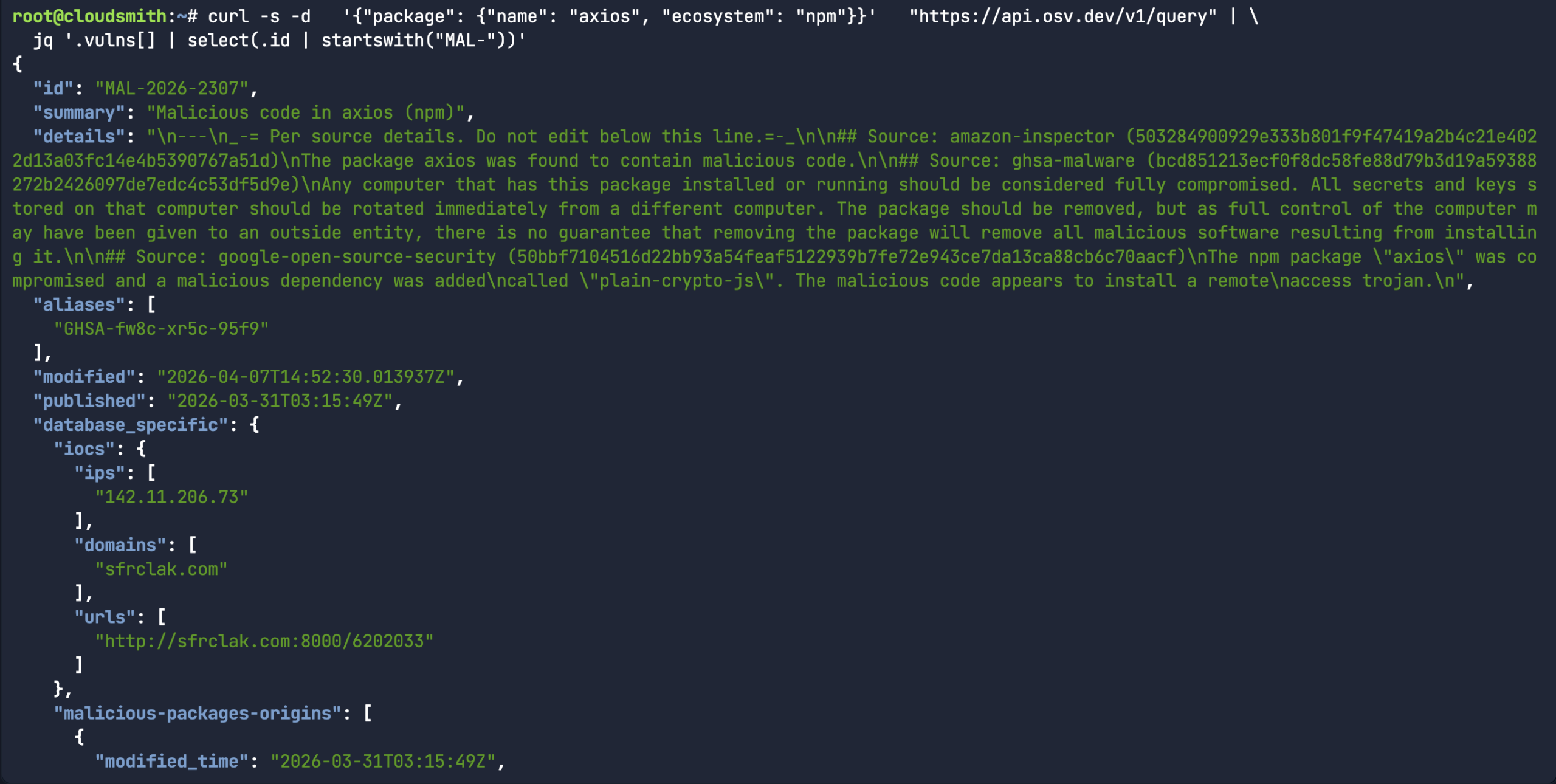 Or in the case of the
Or in the case of the 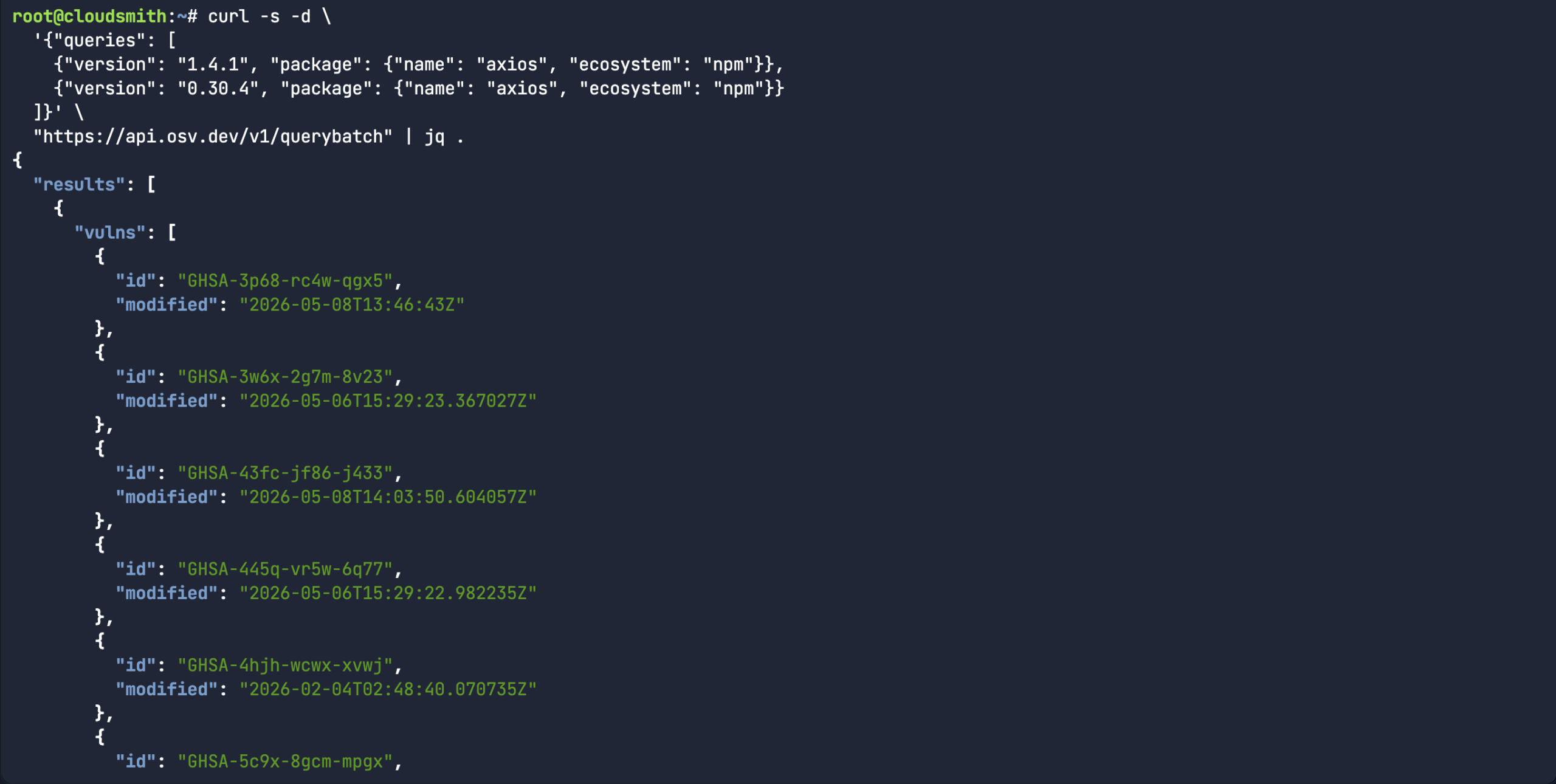
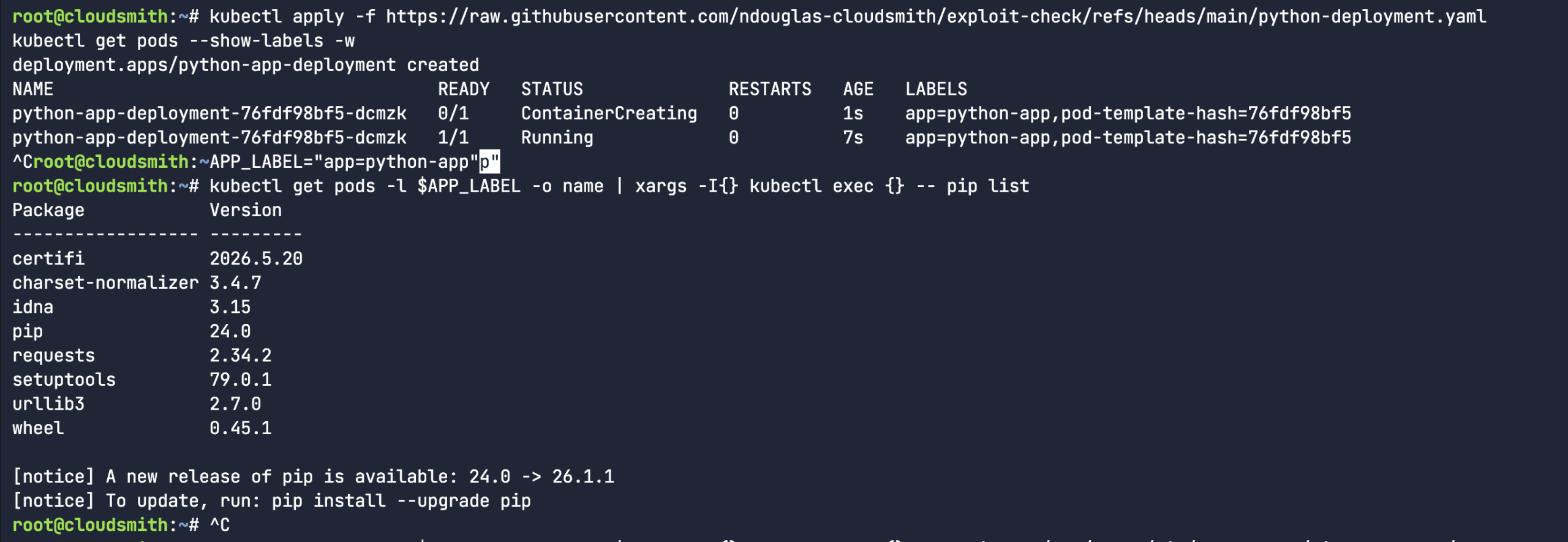 So, I proceeded to create a fake python library (rather than downloading an actual malicious software package). I mean, the package name and version were real, but I fabricated the entire content of the package. It’s a totally dummy package – as you can see from the below echo commands. Let’s see if our custom
So, I proceeded to create a fake python library (rather than downloading an actual malicious software package). I mean, the package name and version were real, but I fabricated the entire content of the package. It’s a totally dummy package – as you can see from the below echo commands. Let’s see if our custom 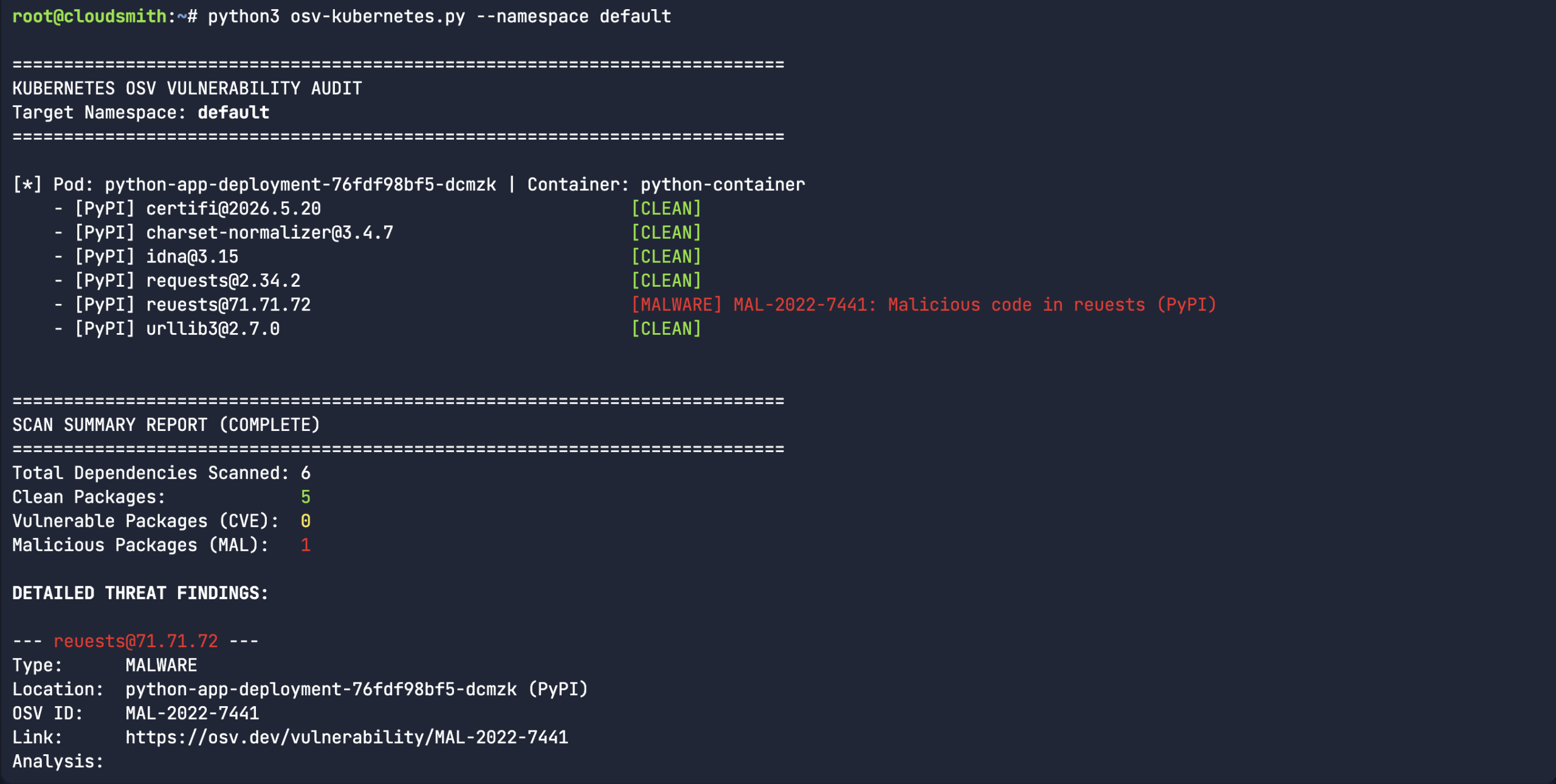 So, we created a fake typosquatted Python package. “
So, we created a fake typosquatted Python package. “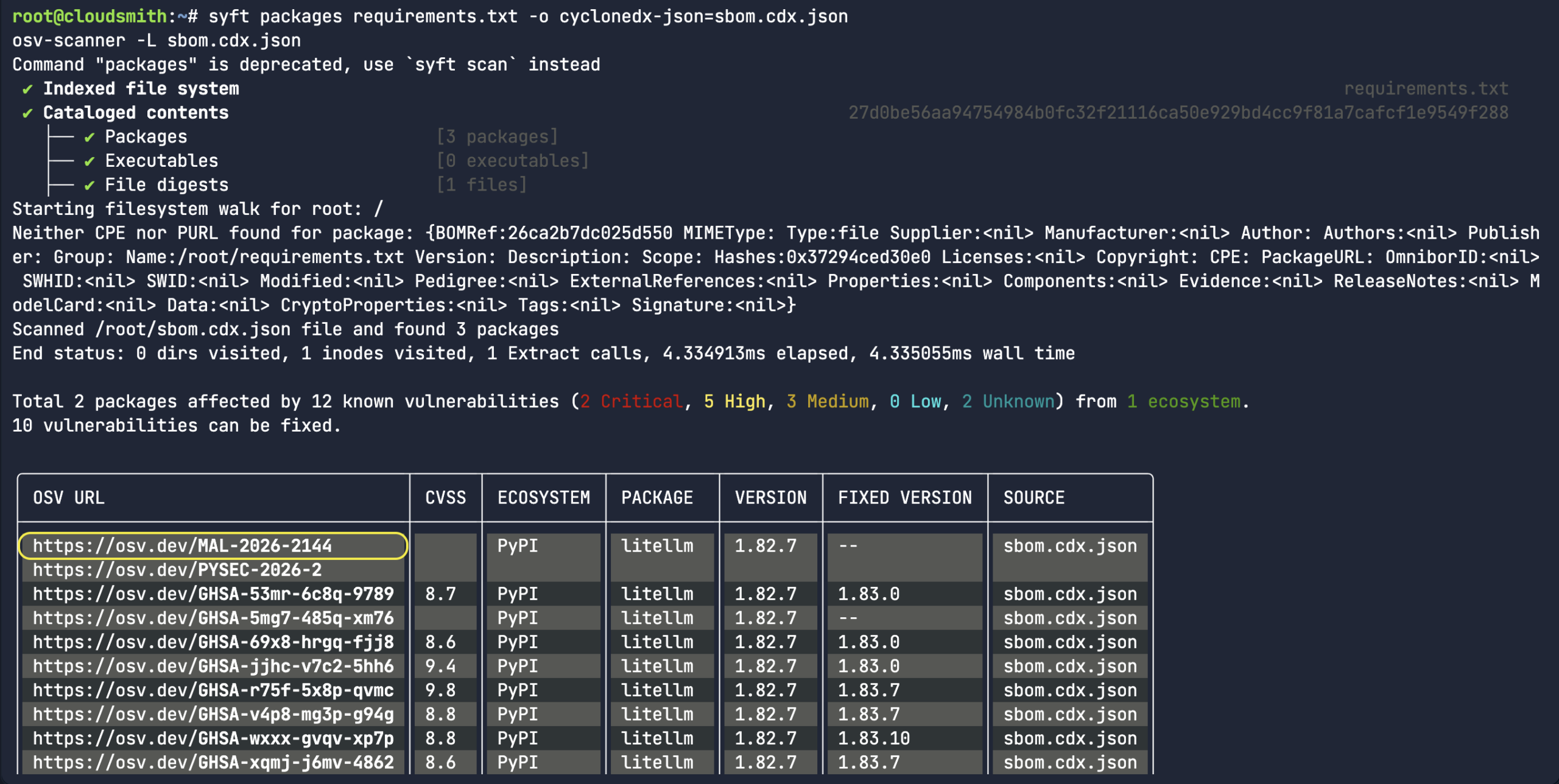
 Nigel Douglas is the Head of Developer Relations at Cloudsmith. He champions Cloudsmith’s developer ecosystem by creating compelling educational content, engaging with developer communities, and promoting software supply chain security best practices. Nigel helps build and shape the DevOps community through events, tutorials, and innovative programs.
Nigel Douglas is the Head of Developer Relations at Cloudsmith. He champions Cloudsmith’s developer ecosystem by creating compelling educational content, engaging with developer communities, and promoting software supply chain security best practices. Nigel helps build and shape the DevOps community through events, tutorials, and innovative programs.
 Christopher Robinson (aka CRob) is the Chief Technical Officer and Chief Security Architect for the Open Source Software Foundation (OpenSSF). With over 25 years of experience in engineering and leadership, he has worked with Fortune 500 companies in industries like finance, healthcare, and manufacturing, and spent six years as Program Architect for Red Hat’s Product Security team.
Christopher Robinson (aka CRob) is the Chief Technical Officer and Chief Security Architect for the Open Source Software Foundation (OpenSSF). With over 25 years of experience in engineering and leadership, he has worked with Fortune 500 companies in industries like finance, healthcare, and manufacturing, and spent six years as Program Architect for Red Hat’s Product Security team.

 Helen Woeste joined OSTIF in 2023, coming from a decade of work experience in the restaurant and hospitality industries. With a passion (and degree) for writing and governance structures, Woeste quickly transitioned into an operations and communications role in technology.
Helen Woeste joined OSTIF in 2023, coming from a decade of work experience in the restaurant and hospitality industries. With a passion (and degree) for writing and governance structures, Woeste quickly transitioned into an operations and communications role in technology. 


 Devashri Datta is an AI & Software Supply Chain Security Researcher. Security researcher and enterprise security architect focused on software supply chain security, DevSecOps automation, and security governance at scale. Research areas include SBOM governance, vulnerability intelligence (VEX), Third-Party Notice (TPN) analysis, AI-assisted risk modeling, and security exception management in cloud-native environments under compliance frameworks such as SOC 2, ISO 27001, and FedRAMP.
Devashri Datta is an AI & Software Supply Chain Security Researcher. Security researcher and enterprise security architect focused on software supply chain security, DevSecOps automation, and security governance at scale. Research areas include SBOM governance, vulnerability intelligence (VEX), Third-Party Notice (TPN) analysis, AI-assisted risk modeling, and security exception management in cloud-native environments under compliance frameworks such as SOC 2, ISO 27001, and FedRAMP.